🕤︎ - 2024-04-15
Today I counted the number of NNTP-servers I have implemented for different purposes over the years.
I wonder if I qualify for Guinness book of records - I have implemented 5 different NNTP-servers:
- d-a-d.com discussion forum (Perl)
- Feedbase - RSS/Atom reader (Perl)
- Lantern - blog engine (Haskell)
- olduse.net - nntp time travel (Haskell)
- Illuminant - ActivityPub server (Haskell)
Some years before implementing Illuminant I also sketched up an NNTP-based microblogging system, which hasn't been implemented (yet?)
🕚︎ - 2024-03-31
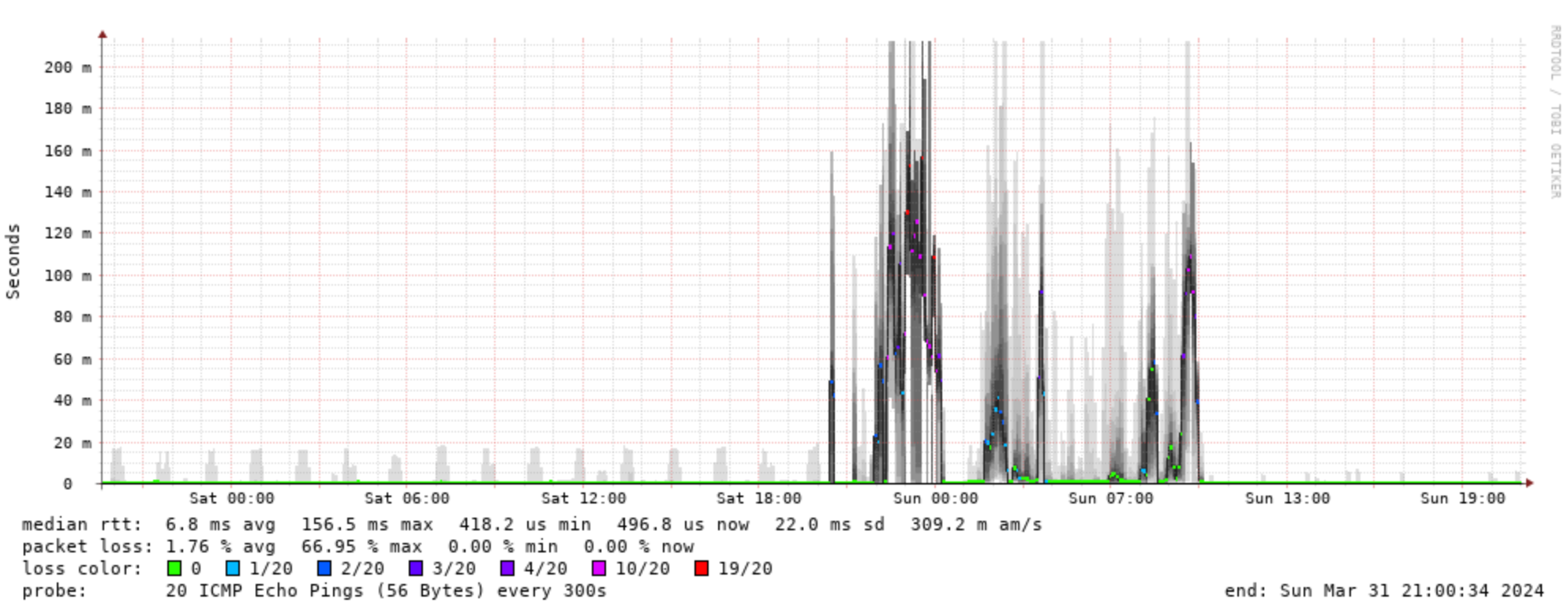
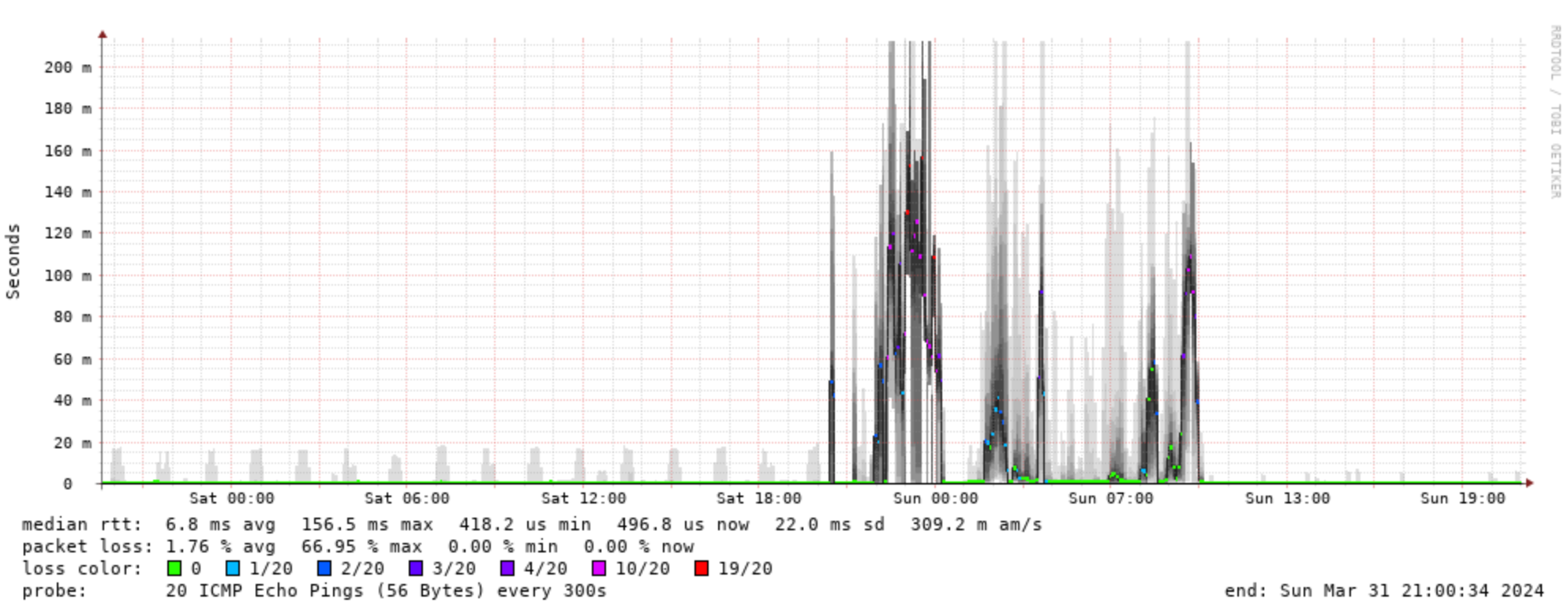
Yesterday evening my home router started acting up. Instead of ping
showing a latency of a couple of ms it went up to hundreds, and on top
of that it started dropping 40-80% of the packets.
I tried turning it off and on again, wildly guessing that my ISP maybe
had done some kind of upgrade or something.
It started up nicely, but then bogged down again. After a while I
looked at the smokeping graph, which confirmed that something was
wrong:
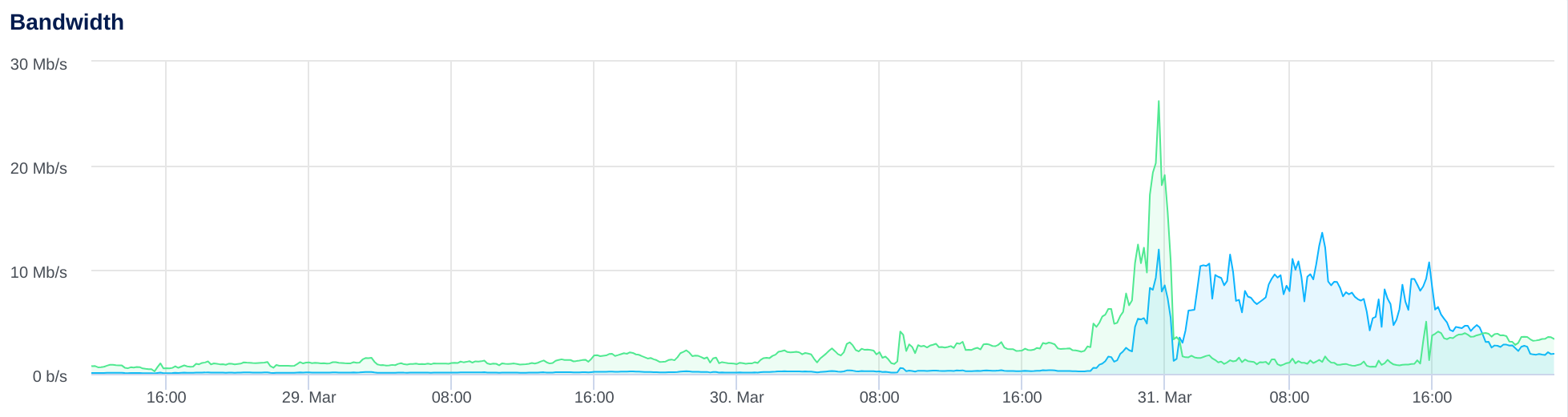
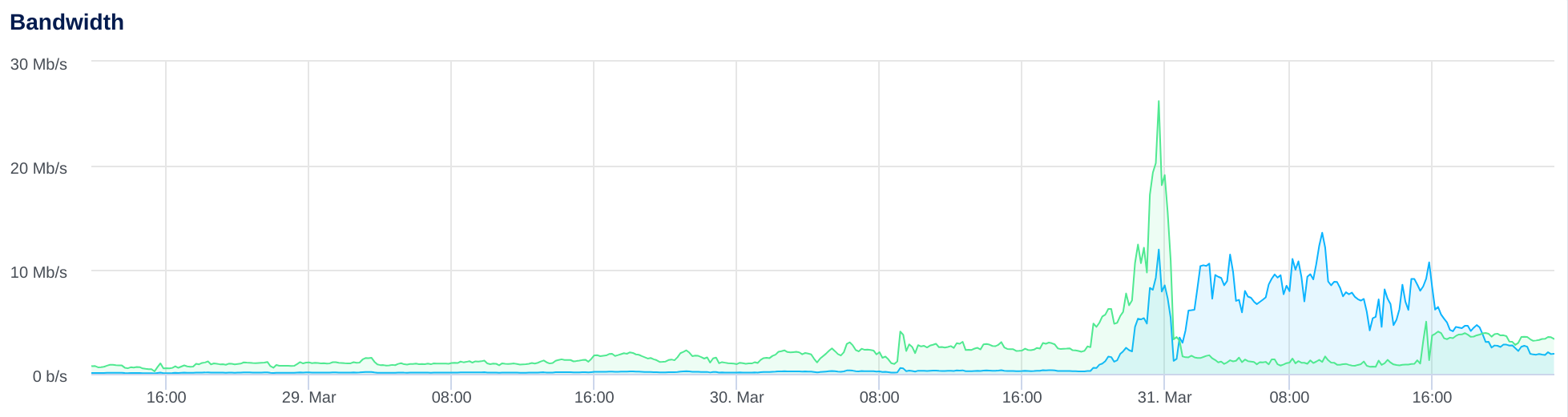
I noticed that on my three DNS servers, one behind this router and two
on VPS's, named was in the top of the CPU usage list. Hm.
ngrep'ing traffic on port 53 revealed a single IP doing a lot of
requests for asjo.org. As in thousands.
I even got a warning from one of the VPS hosters telling me about the
sudden spike in outbound traffic.
I started dropping the packets from that IP on the servers, and in the
router, the outbound traffic disappeared, and my router no longer
suffered. Yay!
It seems like a weird low-key DoS attack, but it's kind of hard to
understand. It's not that disruptive - luckily - and it seems to come
from one IP-address only.
Well, almost. After I started dropping all packets from that IP,
another one showed up as excessively active, so I started dropping
packet from that one as well. Almost as soon as I did, the barrage
from this second IP stopped completely.
The first IP, however, is still sending UDP packets at some 1-2 MBps
to each VPS, here more than 24 hours later. Go figure.
I know that various people mistake my domain asjo.org for something
else from time to time (when I had a Twitter account @asjo that also
happened quite a bit), but what this IP-address - apparently somewhere
in central China - has against my DNS servers, I can't tell. It's odd.
🕥︎ - 2024-03-29
Tried to watch Atomic Blonde tonight, as it is available on Danish National Television - I bailed after 30 odd minutes; it wasn't for me.
🕥︎ - 2024-03-12
I have mentioned The Unix Heritage Society mailing list before - fun stuff comes by on it from time to time.
Today Douglas McIlroy replied to a thread about the early Unix rand() routine and who had written a funny note in the documentation, recalling an early story of password breaking:
When Ken pioneered password cracking by trying every word in word lists at hand, one of the password files he found plenty of hits in came from Berkeley. He told them and they responded by assigning random passwords to everybody. That was a memorable error. Guessing that the passwords were generated by a simple encoding of the output of rand, Ken promptly broke 100% of the newly "hardened" password file.
Ken Thompson replied:
i wrote the generator.
dmr or rhm wrote the comment.
🕕︎ - 2024-02-24
A staple of usenet and email is the .signature. I just had a little peek at a usenet archive to find some of my old ones.
.
-*-
Adam_Sjoegren@thesystem.bbs.bad.se \O_ BBS +45-31-354775
Copenhagen, Denmark | ANet betatester
GCChost support DK / \ FidoNet 2:230/149
GCChost was software for running a FidoNet node - it was very configurable through ARexx, and at some point I think I started handling licenses for Denmark (the author was in Italy).
ANet was BBS software from Sweden that I was running, it had a cool interface where navigation was done by typing "shortest command prefix", automatically figured out by the software.
My BBS was called "The system", with that capitalization, for some... uh... artistic or otherwise self-indulgent reason.
Adam Sjoegren Interstellar Navigation DLG BB/OS 24h
Copenhagen, Denmark asj@inav.bbs.bad.se +45 31354775
EMS/GCCh support DK * Powered by AGA and 040 * 16.8k USR Dual
GCChost was replaced by EMS, by the same author, which was designed to handle other types of mail/news systems than FidoNet - we all had email and usenet envy in those days - so it was attractive.
By this time I had changed the name of my BBS to Interstellar Navigation, and I had changed software to the Canadian developed DLG, and it was running on my Amiga 4000, which I was very proud of. It was very expensive as well.
I kind of liked the little stick figure in the older .signature, and have taken to putting a variant in motd on my machines these days, eg:
$ ssh virgil
Linux virgil 6.1.0-18-amd64 #1 SMP PREEMPT_DYNAMIC Debian 6.1.76-1 (2024-02-01) x86_64
_.
\O_. virgil: PC, Copenhagen
| AMD Ryzen 5 2400 GE (8 cores)
._/_\_, 64G memory, 1.9T disk
o o
Last login: Sat Feb 24 15:20:02 2024 from 192.168.1.102
Just for fun.
🕙︎ - 2024-02-21


The Danish National Museum has started advertising the upcoming exhibition about Denmark during the last 40 years seen through the band D-A-D, which turns 40 the day the exhibit opens, March 3rd, 2024.
The weekend after the opening there is a series of talks at the museum as well!
🕡︎ - 2024-02-14

GNU Emacs,
Debian GNU/Linux,
Linux,
Gnus,
X.Org,
Postfix,
GHC,
PostgreSQL,
OpenSSH,
Firefox,
Apache,
ejabberd,
Dovecot,
git,
GnuPG,
XMonad,
jabber.el,
Magit,
rdiff-backup,
LaTeX,
Gimp,
VLC,
Syncthing,
Sakura,
chrony,
Fail2ban,
WeeWX,
DejaVu fonts,
ripgrep,
lirc,
MPD
Flameshot,
lots of GNU,
the list goes on and on - thanks everybody!